Slot Capitan – The Best Slot Website in India
Welcome to Slot Capitan – Your Ultimate Slot Destination in India!

At Slot Capitan, we bring you the best of the world of slots right at your fingertips. We specialize in providing comprehensive slot reviews, offering demo games, collecting exclusive casino bonuses, and much more.
Are you eager to explore the thrilling world of slot games? Look no further! Slot Capitan is here to guide you through the exciting realm of online slots.
Uncover the Best Slot Reviews
Our team of experts works tirelessly to bring you detailed and unbiased reviews of the finest slot games available. From classic slots to the latest video slots, we’ve got you covered. Our reviews highlight the key features, gameplay, and winning potential of each slot, allowing you to make informed choices.
Try Out Demo Games
Want to test the waters before diving in? We offer a wide selection of demo games that allow you to play for free, without risking any real money. It’s the perfect way to get a feel for different slots, explore their unique themes, and experience the excitement they offer.
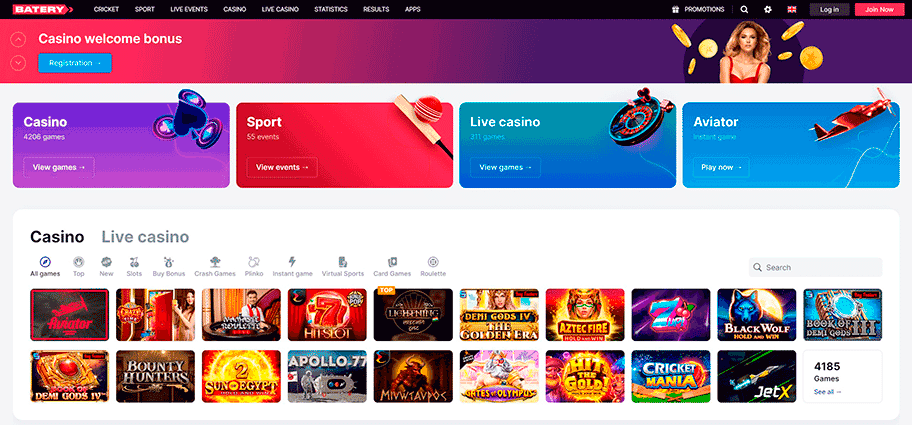
Collect Exclusive Casino Bonuses
As a Slot Capitan member, you gain access to exclusive casino bonuses. We scour the internet to find the most lucrative offers, including welcome bonuses, free spins, and deposit matches. By taking advantage of these bonuses, you can maximize your playing time and increase your chances of hitting those big wins.
The Best Slot Website in India
At Slot Capitan, we take pride in being the premier slot website in India. Our dedication to providing top-notch content, unrivaled slot reviews, and a user-friendly experience sets us apart from the rest.
Join us today and embark on an unforgettable slot adventure with Slot Capitan – the ultimate destination for slot enthusiasts in India!
- Comprehensive slot reviews
- Demo games to try out
- Exclusive casino bonuses
- The best slot website in India